" UPDATE January 2022: old review kinda sucked, I'm rewriting it. LibreWolf is to Firefox what Ungoogled-Chromium is to Chrome. At least, so it seems, but it does not take a strict stance against unsolicited requests like Ug-C does (which is also my view - zero unsolicited requests is optimal). It includes the uBlock Origin addon by default (instead of the much superior uMatrix), and automatically updates the lists for it - as well as making a request to Mozilla's servers for their Tracking Protection. Otherwise, LibreWolf is not doing anything special, just changing some settings (which can also be accomplished by the many user.js files floating around). Their issue tracker is on gitlab which is Cloudflared and doesn't work in Pale Moon; this does not affect the browser directly, but shows the developers don't respect the users or care about their privacy. Packages for some distros, Windows and macOS exist - as well as an AppImage if your distro isn't on the list. Overall, this is the way to go if you want Firefox without (most of) the privacy violations. But - since they've only got five devs on the team - LibreWolf will always be dependent on Mozilla and unable to reverse any of their major s****y decisions, so watch out. Let me reiterate, this is nothing more than Firefox with a few settings changed and uBlock Origin added on top."
https://digdeeper.neocities.org/articles/browsers#librewolf
and to balance it out, icecat does have some flaws:
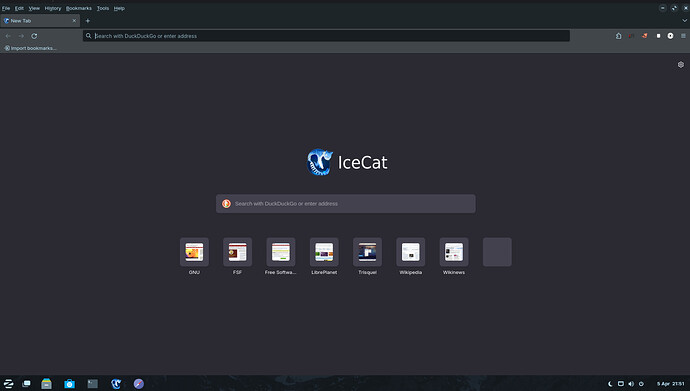
"UPDATE December 2023: Someone has compiled IceCat version 115 for Linux, Windows and Mac (the last officially supported version is still the ancient and insecure 60). And so, time for a new review. Brace yourself, for I will (maybe surprisingly) have a lot to say. Anyway, IceCat is still Firefox, but scrubbed of most unsolicited connections (but still has OCSP, and captive portal detection, it seems). With the updated version, the resource usage has also been "updated" to now clock at about 300mb RAM (compared to the 120 of old versions). What makes IceCat unique are the privacy-enhancing addons coming along for the ride. IceCat uses the extension Privacy Redirect to...well, redirect big tech services to their more user respecting replacements (Invidious, Nitter, etc). Not much to say there, it is a good and obvious addition - so let's move on.
As is tradition, IceCat includes LibreJS, that I don't really like; again, it has the same flaws as always, meaning lots of resource usage and the arbitrary allowance of "trivial" scripts. Additionally, it now brings with it three more extensions hoping to fix certain sites, that LibreJS would otherwise break. Is it really a viable approach to write replacements for scripts on every site which lacks the "right" license? Funnily enough, IceCat's LibreJS implementation includes whitelists for reddit scripts - lol! And the first script there even looks quite nontrivial to me. If the licensing issue is that important to you, then stop giving passes to big tech just because they're big.
Another included addon is JShelter, invented to prevent JavaScript-based fingerprinting by reporting fake data to certain JS functions. By this, it is trying to convince the site you're visiting that you're a different person than before. It's too complicated to explain it all here but let's just say that this approach is quite leaky in that it needs just one thing that cannot be faked or can somehow be detected by the fingerprinter to foil your attempts. JShelter admits it eg here (archive) (MozArchive):
No. We currently do not have a consistent method that spoofs fonts reliably. If you are concerned about font enumeration, you can track the relevant JShelter issue.
I don't believe that this approach is very fruitful. JS is just too complicated, it's a real language that has access to everything that the browser is doing. And you can't "enumerate badness" well enough to block fingerprinting reliably this way. For another example, see Advanced Tor Browser Fingerprinting (archive) (MozArchive). Keep in mind that even if you like JShelter's approach, it (by default) is concerned only with fingerprinting prevention - it still lets the browser execute JS functions that might be malicious. However, I guess there is no harm in JShelter being used - at least it provides some protection if you're going to be enabling JavaScript anyway. Blocking JS execution completely would be more effective, though; there's no need to fake data for functions that don't run at all (but of course, then you can't do anything that requires JS).
But this is still not that great against first party fingerprinting; you're connecting to the first party domain regardless, so it can use your user agent, IP, OS, etc. to add to the fingerprint. There is no perfect way to prevent first party fingerprinting; remember, you have to convince the fingerprinter that you're a different person than before, and any one piece of data can blow your cover. The best way is to use an entirely different physical computer every time you visit that site, or at least a different OS / browser combination and also change your IP. For third party fingerprinting, it is easy - just block the connections; if there is no connection made, there is nothing to fingerprint you by.
And so, we reach the final addon included in IceCat, namely the rarely seen TPRB (Third Party Request Blocker) - which actually has a lot of functionality not related to its name. For one, it is able to block Cloudflare, and can also redirect the pages behind it to their Web Archive versions - so it's a replacement for the abandoned Block Cloudflare MitM Attack. It can block specific CSS, JS functions, as well as file type downloads and do many many other things I don't care to list here. But the problem is that the defaults are very permissive - whitelisting YouTube, and again Reddit, as well as exposing you to the Cloudflare MitM rp (a decision I cannot justify at all). If you have the functionality to prevent such serious security vulnerability, why not enable it by default? In terms of its main functionality (being a proto-uMatrix), TPRB does block third party requests by default - but you can only allow them selectively by domain, and not by type (so either all or none from a certain domain). Also, all third party CSS is let through - pretty much refuting the name of the addon (though you can change this, but we're talking about the defaults here).
And this exposes the problem with the entirety of IceCat's design - which is that its target audience is the normie, and not the hacker. That's why JS is enabled by default, and then there are all those measures attempted to contain it. It even gives up the FSF's favorite licensing crusade just to let people use reddit. And though it includes the extremely powerful TPRB, again the defaults are so permissive as to make most of its functionality irrelevant until the user digs deep into the settings. Overall, IceCat just does not know what it wants to be; it is a weird mish-mash of blocking undesirable things but also allowing stuff through the shields arbitrarily for convenience. It would be nice to finally have a modern browser perfectly mitigated by default, but IceCat is not it. It - like all other FF forks - is also on Mozilla's leash, and this won't ever change."
https://digdeeper.neocities.org/articles/browsers#icecat
Table of comparison:
| Browser / Feature |
Spying |
Engine |
Extensions |
GUI library |
Source code |
RAM usage |
| Mozilla Firefox |
High |
Gecko |
WebExt |
GTK3 |
Yes (Full) |
~260MB |
| GNU IceCat |
Mild |
Gecko |
WebExt |
GTK3 |
Yes (Full) |
~300MB |
| LibreWolf |
Mild |
Gecko |
WebExt |
GTK3 |
Yes (Full) |
~260MB |
| Waterfox |
Medium |
Gecko |
WebExt |
GTK3 |
Yes (Full) |
~300MB |
| SeaMonkey |
Medium |
Gecko |
XUL |
GTK3 |
Yes (Full) |
~120MB |
| TOR Browser |
Mild |
Gecko |
WebExt |
GTK3 |
Yes (Full) |
~260MB |
| Google Chrome |
High |
Blink |
WebExt |
GTK3 |
No (or not full) |
~170MB |
| Iridium Browser |
Mild |
Blink |
WebExt |
GTK3 |
Yes (Full) |
~170MB |
| Ungoogled-chromium |
None |
Blink |
WebExt |
GTK3 |
Yes (Full) |
~170MB |
| Brave Browser |
Medium |
Blink |
WebExt |
GTK3 |
Yes (Full) |
~170MB |
| Dissenter Browser |
Medium |
Blink |
WebExt |
GTK3 |
Yes (Full) |
~170MB |
| Opera |
High |
Blink |
WebExt |
GTK3 |
No (or not full) |
~260MB |
| Vivaldi |
Medium |
Blink |
WebExt |
GTK3 |
No (or not full) |
~290MB |
| Pale Moon |
Mild |
Goanna |
XUL |
GTK2 |
Yes (Full) |
~100MB |