So seems bug is fixed in new updated version/s.
I have just used Synaptic to see what version of ClamAV I have on ZorinOS 15.3 Core. It appears to be a older version than the update versions mentioned in your post above.
I run ClamAV using the ClamTK UI, installed from the Software store.
I wonder if @AZorin @zorink are aware of this vulnerability issue with ClamAV. I hope they will be pushing ClamAV updates as security updates for both Z15 and Z16 that are currently supported?
ClamAV is not included in Zorin OS. As it is something that a member must seek out for themselves, it is those members responsibility to keep their own installed software up to date.
That's strange as when I first installed Z15 it was there, I just installed ClamTK and it worked.
It may be that APT supplied the necessary dependencies,. A quick review of the Zorin OS repository contains no CLAM software for Xenial, Bionic or Focal:
https://launchpad.net/~zorinos/+archive/ubuntu/stable/+packages
OK. I have been doing some investigating.
By way of a thread on the old Zorin Forum I was directed to @swarfendor437 's Unofficial Manual page 127, which states:-
"This is the AV software for GNU/Linux – installing ClamTk not only installs the back end of Clam AV but also It’s graphical front-end shown in screen shot ..."
So I assume from that, it was ClamTK from Software store that pulls in ClamAV.
ClamTK in Software store never seems to get updated.
Originally Clam AV was a coomand line utility.
True it still is. You don't have to use the ClamTK UI to use ClamAV.
It is the issue of updates that is of concern right now.
I don't use Store on any platform/OS. I will either use Synaptic, or occasionally Apper on KDE. I also avoid Discover on Plasma as it is just a KDE variant of Software/Store.
So then you are a geek programmer what using a mostly terminal in life and customize themes?
Some good advice here.
You need to install clamav-daemon as well as the packages listed in Synaptic. When run in terminal on Devuan in terms of installing clamav via terminal it states database 28618 is up to date - which is what clamtk showed when it was installed - this is the update number, not the number of signatures which are given after the version number:
Mon Feb 20 21:21:20 2023 -> daily.cvd database is up-to-date (version: 26818, sigs: 2021302, f-level: 90, builder: raynman)
Just done some further searches and found this:
https://tfun.org/2023/02/17/cisco-clamav-rce-html/
This would be also the 'same' issue as that facing 'Barracuda portal'.
Basically Cisco and Barracuda products have used ClamAV within their own products and whilst they can solve the issues potentially facing them, they cannot 'mend' ClamAV - they have repaired their products to be secure from the vulnerability discovered. My only other concern about this is an android application I use on my Fairphone - Hypatia, which uses the ClamAV engine!
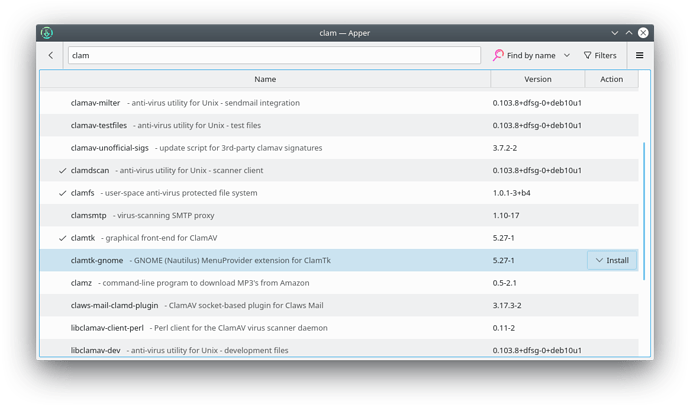
I've just launched Apper on Devuan and found some other interesting packages, clamfs (have installed), and clamtk (again). Also noticed there is a separate clamtk for gnome!:
On ClamAV website there are 2 LTS versions avalable. The older being ClamAV 0.103.8. which is patch version addressing the vulnerabilities mentioned in the OP.
When I checked my Synaptic PM listing for clam yesterday, it only showed the previous patch version 0.103.6. (Please note I am still running Z15.3, not Z16.2. I am planning to wait for Z17 before updating what is a rock solid version of ZorinOS.)
I assume the latest ClamAV patch version 0.103.8 has not trickled through to updates yet?
It has now!
Software Updater included clam 0.103.8 today. So now I have the latest patched version of ClamAV (on Z15.3) that resolves those security vulnerabilities. ![]()
clamav has now been patched according to Linux Security:
Linux razy repairing Bugs.
I removed ClamAV that was installed via Devuan repo and installed the .deb from ClamAV sie using Gdebi. Upon install it warns of an older version in the repo.
These vulnerabilities in ClamAV were patched in the repositories back in February, so you should be protected if you've installed the latest updates from the Software Updater. You can find more information about this newer patched package here: