Telegram .deb installer:
http://archive.ubuntu.com/ubuntu/pool/universe/t/telegram-desktop/telegram-desktop_2.0.1+ds-1build1_amd64.deb
More trouble than it is worth.
RedHat has broken our trust as often as MS and almost as often as Ubuntu.
Flatpaks end up double sandboxed, which requires users to have to undo some of it just to get some apps to work. Which... you already know. What point is that sandbox when it gets in your way?
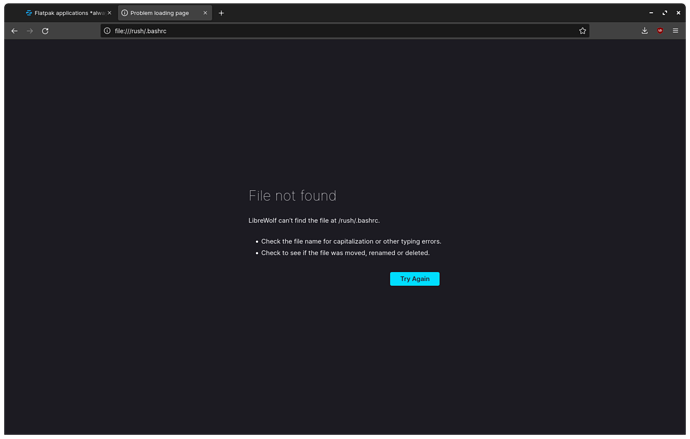
Especially when security-wise - it is a sham. Easily bypassed with echo download_and_execute_Malware >> ~/.bashrc
In spite of the claim that Flatpak is the most up to date: It isn't. In fact, for security updates, flatpak lags behind. Flatpaked Gimp for example had the critical vulnerability "shell in the ghost" which was fixed in flatpak about one month after linux distributions had applied the patch.
Or this patch which was a Major Security Update as it allowed using any Flatpak containing an suid binary to grant access to the hosts ROOT:
The Flatpak developers eventually got around to patching this... late... And commented merely it was:
This is a minor security update, matching the behaviour on master
where we avoid ever creating setuid files or world-writable
directories. However, the fix is more localized and does not
require a new ostree.
A "minor secureity update," they said. Minor. Trust -> Gone...
They were more concerned with trying to save face than trying to ensure the security and safety of users. Not... that this is unusual for RH but...
Just my 45 cents.